|
|
|
|
|
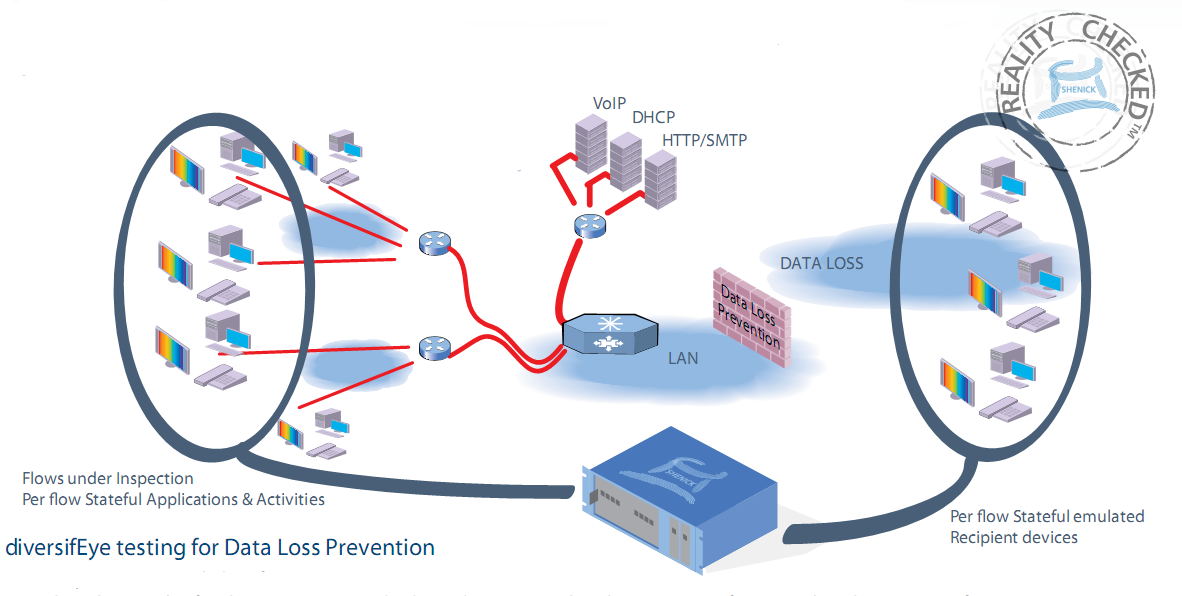
Data Loss Prevention (DLP)
Data Loss is an every day threat within all organizations. The leaking of confidential data ultimately results in a loss of revenue. A quarter of all Data Loss is widely attributed to the use of applications such as Voice, Email, Instant Messaging, Social Networks, Blogs, P2P and Videos. A common approach adopted to preventing Data Loss is to use sophisticated data detection algorithms and the deployment of systems to control applications attempting to access the outside world.Data Loss is an every day threat within all organizations. The leaking of confidential data ultimately results in a loss of revenue. A quarter of all Data Loss is widely attributed to the use of applications such as Voice, Email, Instant Messaging, Social Networks, Blogs, P2P and Videos.
Why test DLP with diversifEye?
diversifEye is utilized to test and verify Data Loss Prevention (DLP) systems and algorithms through emulating thousands of “good” users with real or stateful TCP and UDP based applications and a small number of “bad” users.
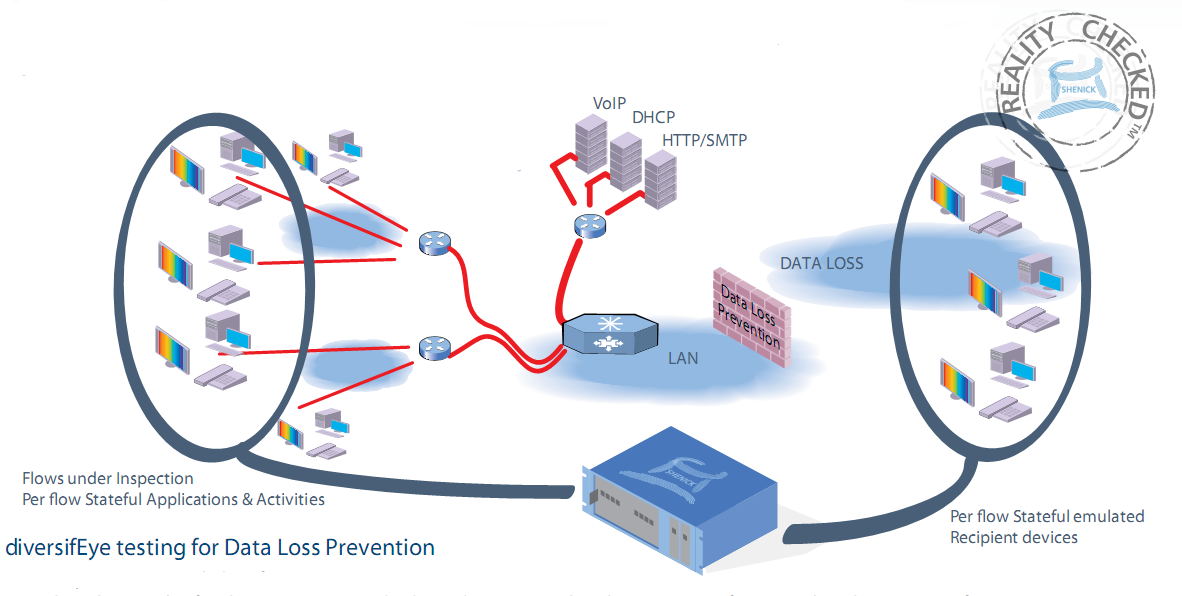
diversifEye's Per Flow metrics can rapidly determine if the "bad" users activities are properly identified and blocked
diversifEye testing for Data Loss Prevention :
-
Per Flow, Emulation and Identification –
Emulate thousands of real users running multiple applications. Within the vast array of users and applications, configure a single user to send out ‘confidential’ information periodically.
-
Real World Traffic Flows –
More than just traffic simulation or packet stuffing, emulate large volumes of real or stateful traffic flows, such as POP/SMTP, HTTP, VoIP, Telepresence, VoD, P2P, IM, etc.
-
Configurable Unique Properties –
Configure individual MAC address, IP address, VLAN Tags, ToS/DiffServ right through to Port assignments. Utilize a mix of IPv4, IPv6 and Dual-Stack Lite sessions concurrently.
-
Fully Customizable Content –
Customize content for Email, HTTP and FTP. Send customizable emails with content attachments such as docs, pdf, zip files, etc. Generate email with confidential information such as social security numbers.
|
|
|
|